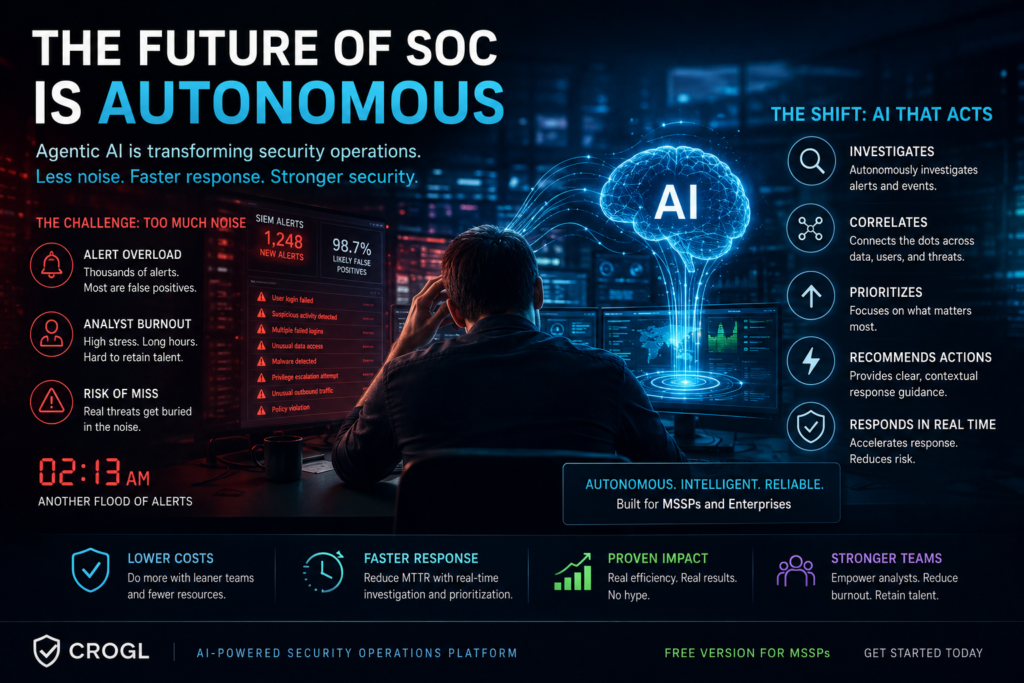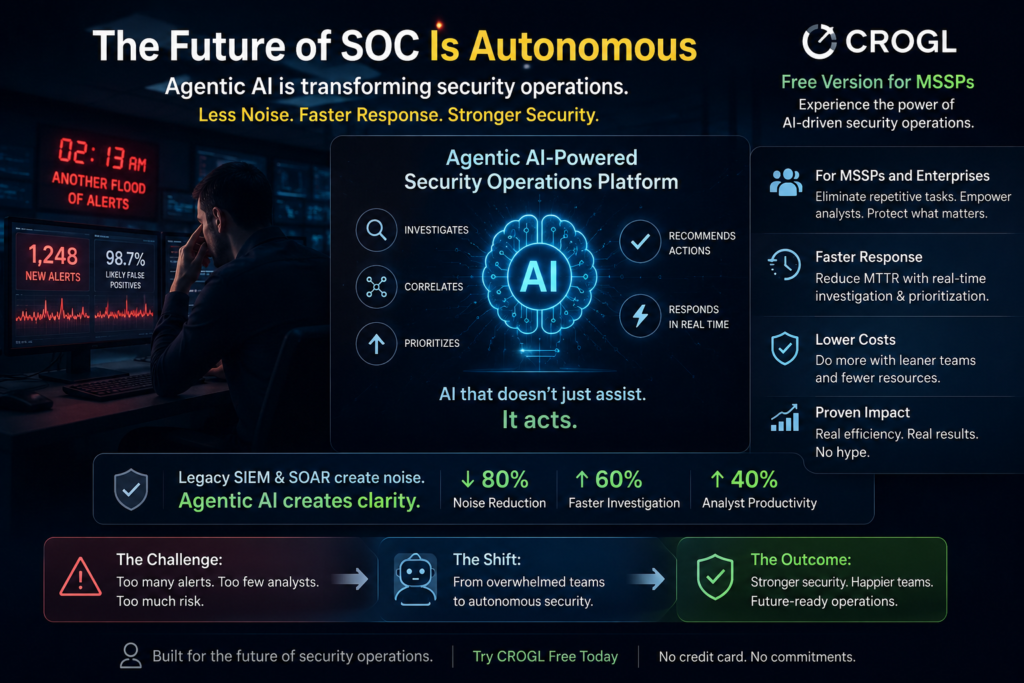
At 2:13 a.m., a SOC analyst stares at another flood of alerts lighting up the dashboard. Most will be false positives. A few may signal real danger. The challenge is no longer just detecting threats—it’s surviving the sheer volume of security noise without burning out teams or missing critical attacks. That pressure is exactly why the cybersecurity market is rapidly shifting toward the AI security operations platform model.
CROGL’s announcement of a free version of its agentic AI-powered platform for MSSPs is more than another product launch. It signals a growing movement toward autonomous security operations where AI doesn’t merely assist analysts—it actively investigates, correlates, prioritizes, and recommends actions in real time. For U.S. IT decision-makers, this trend arrives at a crucial moment. Security teams are stretched thin, hiring skilled SOC analysts has become increasingly expensive, and attackers are moving faster than traditional workflows can handle.
The rise of agentic AI cybersecurity platforms reflects a broader industry realization: legacy SIEM and SOAR systems often create operational overload instead of reducing it. Enterprises and MSSPs are now demanding tools that eliminate repetitive tasks while improving response speed and accuracy. CROGL’s free offering introduces a low-friction way for providers to test autonomous investigation capabilities without committing to major upfront costs.
That matters because cybersecurity purchasing behavior is changing. Decision-makers are increasingly skeptical of AI hype. They want measurable efficiency gains, lower response times, and operational clarity—not flashy automation claims. Platforms that can prove real-world impact are positioned to dominate the next generation of security operations.
What Is an AI Security Operations Platform?
An AI security operations platform combines artificial intelligence, automation, threat intelligence, and behavioral analysis into a centralized system that helps security teams detect and respond to threats more efficiently. Unlike traditional tools that mainly collect and display alerts, AI-native platforms actively analyze security events and assist with investigations.
Modern platforms use technologies such as:
- Machine learning
- Behavioral analytics
- Natural language processing
- Autonomous investigation engines
- Threat correlation automation
The newest evolution is agentic AI, which goes beyond simple automation. Traditional automation follows fixed workflows. Agentic AI adapts dynamically based on context, available data, and evolving threats. In practical terms, it behaves more like a digital analyst than a scripted tool.
For IT decision-makers, this distinction matters because operational efficiency is becoming a business requirement rather than a technical luxury. According to industry reports, security teams in the U.S. face thousands of alerts daily, with many organizations lacking sufficient staff to investigate them effectively. The result is alert fatigue, slower response times, and increased breach risk.
AI-powered SOC platforms aim to reduce these pressures by:
| Capability | Traditional SOC Tools | AI Security Operations Platforms |
|---|---|---|
| Alert Correlation | Mostly manual | Automated and contextual |
| Threat Investigation | Analyst-driven | AI-assisted or autonomous |
| Response Speed | Slower | Near real-time |
| Scalability | Limited by staff | Highly scalable |
| Analyst Workload | High | Reduced |
The biggest appeal for MSSPs is scalability. Managed providers must support multiple clients simultaneously while maintaining profitability. AI-driven investigation systems allow smaller teams to manage larger environments without sacrificing response quality.
Why CROGL’s Free Platform Is Turning Heads
Free products in cybersecurity are rarely truly “free.” Usually, they serve as strategic entry points into larger ecosystems. CROGL’s decision to launch a free version of its platform appears designed to accelerate adoption among MSSPs that may otherwise hesitate to experiment with autonomous AI security operations.
That strategy could be highly effective in today’s market environment.
Many MSSPs want AI capabilities but struggle with:
- High licensing costs
- Complex implementation
- Integration headaches
- Unclear ROI
- Fear of operational disruption
By lowering the barrier to entry, CROGL allows providers to evaluate agentic AI workflows with less financial risk. This mirrors broader SaaS trends in the U.S., where freemium adoption models often accelerate enterprise trust and long-term customer acquisition.
The timing also aligns with a severe cybersecurity talent shortage. According to ISC2 workforce studies, the cybersecurity labor gap remains a major operational challenge across North America. Experienced analysts are expensive, difficult to recruit, and increasingly vulnerable to burnout. AI-driven investigation tools are becoming attractive not because companies want to replace humans entirely, but because they need to amplify existing teams.
For IT executives, the value proposition becomes easier to justify when AI helps:
- Reduce mean time to detect (MTTD)
- Improve mean time to respond (MTTR)
- Lower operational overhead
- Minimize repetitive analyst tasks
- Increase analyst retention
The free tier could also pressure competitors. Established SIEM and SOAR vendors may face increased expectations around accessible AI functionality. Buyers are beginning to expect intelligent automation as a standard capability rather than a premium add-on.
Why Agentic AI Is Different From Traditional Security Automation

The cybersecurity industry has discussed automation for years, but many organizations remain disappointed with older automation frameworks. Traditional SOAR systems often require complex playbook creation, constant tuning, and heavy maintenance. In many cases, teams spend more time managing automation than benefiting from it.
Agentic AI changes the equation because it introduces adaptive reasoning.
Instead of rigid workflows, agentic systems can:
- Interpret evolving threat context
- Dynamically prioritize risks
- Generate investigation paths
- Correlate unrelated signals
- Recommend response actions
Think of traditional automation like a train on fixed tracks. It follows predefined routes with little flexibility. Agentic AI behaves more like an experienced investigator navigating changing terrain in real time.
This distinction matters enormously in modern cybersecurity environments where attackers constantly modify techniques. Static workflows struggle against rapidly evolving threats, while adaptive AI models can identify suspicious patterns across multiple data sources faster than humans alone.
Still, skepticism remains healthy—and necessary.
Many IT leaders worry about:
- AI hallucinations
- False positives
- Lack of explainability
- Compliance concerns
- Overreliance on automation
Those concerns are valid. Fully autonomous cybersecurity remains risky without human oversight. The most effective AI security operations platforms position AI as an augmentation layer rather than a replacement for experienced analysts.
The strongest vendors understand this balance. Successful platforms provide transparency into AI reasoning, allow human approval controls, and maintain audit visibility for compliance requirements.
How AI Security Platforms Help MSSPs Scale Faster

For MSSPs, profitability often depends on operational efficiency. Supporting more customers typically requires hiring more analysts, which increases costs and strains recruiting efforts. AI-powered security operations platforms offer a different path: scale through intelligent automation instead of linear staffing growth.
This is where CROGL’s offering becomes strategically important.
An AI-driven SOC environment can help MSSPs:
- Handle larger alert volumes
- Accelerate customer onboarding
- Reduce analyst burnout
- Improve response consistency
- Expand service offerings
Imagine two MSSPs competing for enterprise clients. One relies heavily on manual investigation workflows. The other uses autonomous AI investigation capabilities to streamline triage and response. The second provider can often deliver faster service with fewer staffing constraints.
That operational advantage can directly influence:
- Customer retention
- SLA performance
- Incident response speed
- Profit margins
- Market competitiveness
U.S. businesses are increasingly prioritizing vendors that demonstrate rapid detection and remediation capabilities. With ransomware attacks and supply chain threats continuing to rise, organizations want reassurance that security providers can respond at machine speed when necessary.
The economic pressure is equally important. Labor costs for cybersecurity professionals continue climbing across the United States. AI-enhanced SOC operations may become essential for MSSPs trying to maintain profitability without dramatically increasing client pricing.
Common Mistakes Companies Make With AI Cybersecurity Adoption
Despite the excitement surrounding AI security operations, many organizations approach implementation incorrectly. Buying advanced AI tools without operational alignment often creates more confusion than value.
Common Mistakes to Avoid
| Mistake | Why It’s Risky |
|---|---|
| Treating AI as a complete replacement for analysts | Human oversight remains critical |
| Ignoring integration planning | Fragmented tools reduce effectiveness |
| Focusing only on marketing claims | Real-world testing matters |
| Overlooking compliance requirements | Can create regulatory exposure |
| Deploying without staff training | Limits adoption success |
One of the biggest mistakes is assuming AI automatically fixes poor security hygiene. AI platforms work best when organizations already maintain strong visibility, asset management, and incident response fundamentals.
Another mistake involves chasing hype instead of outcomes. IT leaders should evaluate measurable benefits such as:
- Reduced investigation time
- Faster containment
- Lower false positive rates
- Improved analyst productivity
- Better operational visibility
The most successful deployments combine AI efficiency with experienced human judgment. Security remains both a technical and strategic discipline.
Key Takeaways for U.S. IT Decision-Makers
The launch of CROGL’s free AI-powered platform highlights several larger cybersecurity trends shaping the U.S. market:
Quick Checklist for Evaluating AI Security Platforms
- Does the platform reduce analyst workload?
- Can it integrate with existing SIEM tools?
- Is AI reasoning explainable and auditable?
- Does it improve response speed measurably?
- Are there human oversight controls?
- Can it scale economically for long-term growth?
Pros and Cons of AI Security Operations Platforms
| Pros | Cons |
|---|---|
| Faster threat investigations | Potential AI inaccuracies |
| Reduced analyst fatigue | Integration complexity |
| Improved scalability | Compliance concerns |
| Lower operational overhead | Vendor dependency risks |
| Enhanced response speed | Learning curve for teams |
The organizations gaining the most value from AI cybersecurity tools are not blindly replacing people. They are strategically using AI to remove repetitive work while enabling analysts to focus on higher-level investigations and decision-making.
The Future of Security Operations Is Becoming Autonomous
The cybersecurity industry is moving toward a future where AI systems continuously investigate threats, prioritize risks, and support human decision-making in real time. CROGL’s free platform represents another step toward that autonomous operational model.
For IT decision-makers, the opportunity is significant—but so is the responsibility. AI adoption should focus on measurable operational outcomes rather than marketing excitement alone. Platforms that genuinely reduce analyst fatigue, accelerate investigations, and improve visibility will shape the next generation of security operations centers.
The larger shift is already underway. Enterprises and MSSPs that successfully integrate intelligent automation today may gain a substantial operational advantage tomorrow. Those that delay risk falling behind competitors capable of responding to threats with greater speed, scale, and efficiency.
The cybersecurity battlefield increasingly rewards organizations that can combine human expertise with machine-driven intelligence. Agentic AI is no longer a futuristic concept. It is rapidly becoming a defining feature of modern SOC operations.
FAQs
What is an AI security operations platform?
An AI security operations platform uses artificial intelligence to help detect, investigate, prioritize, and respond to cybersecurity threats more efficiently than traditional manual workflows.
What does agentic AI mean in cybersecurity?
Agentic AI refers to systems capable of acting autonomously based on context and analysis rather than following rigid predefined automation rules.
Why are MSSPs adopting AI-powered SOC platforms?
MSSPs use AI platforms to reduce analyst workload, improve response speed, handle larger alert volumes, and scale operations without dramatically increasing staffing costs.
Can AI replace cybersecurity analysts?
AI can automate repetitive investigations and improve efficiency, but experienced analysts remain essential for strategic decision-making, oversight, and complex threat analysis.
What should IT leaders evaluate before adopting AI cybersecurity tools?
Decision-makers should assess integration capabilities, operational transparency, compliance support, measurable ROI, human oversight controls, and long-term scalability.